Weather issues https://mynorthwest.com/4010489/cliff-mass-warns-of-powerful-storm-approaching-western-washington/ have impacted the region recently. The power at my home was out for a few days but I was able to reach the office. While there I recall one conversation from a colleague "Power outages in India, not just this long." A similar sentiment was express by a Brazilian co-worker. I suppose the outage reflects the pleasure and peril of the Pacific Northwest with its significant old growth and above-ground power lines. One challenge this offered was having to take a 4am PST call from the office to deliver a talk https://docs.google.com/presentation/d/1gbKhl3ncwRm0QB1ZD3xZhjhRFWxUp_dKtdnQemtpoX0/edit?usp=sharing to an open source firmware event in Germany at https://www.ruhr-uni-bochum.de/en.
Part of my Franken-prezo can be seen below. It was pieced together from old public slides spanning CanSecWest '15 in Vancouver BC through Hacker-to-Hacker circa late '23 in São Paulo, Brazil, viz.,
Recently a local university asked me to give their students a talk on BIOS. I agreed on the conditions that it wasn't at 4am PST and that it was in-person. If they had asked last week I would have added the additional proviso of not occurring during a post wind-pocalypse power outage :)
Given this is a blog that purports to cover musings on firmware and UEFI, I figured that I'd note that recent event.
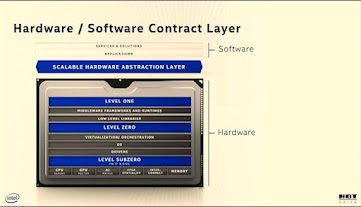
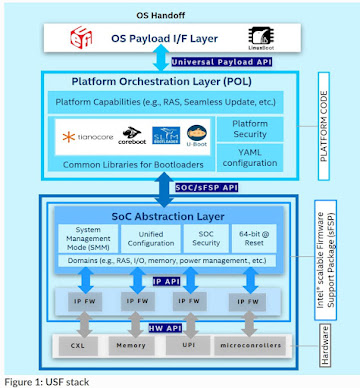
Speaking of firmware, before this talk and continuing in the spirit of this blog's theme there was an Intel blog posting related to the Open Computing Project Summit recently about open source server host firmware https://community.intel.com/t5/Blogs/Tech-Innovation/Data-Center/Advancing-Open-Source-Firmware-on-Intel-Xeon-6-Based-Platforms/post/1636720
As I mentioned in https://vzimmer.blogspot.com/2024/09/reflecting-on-my-time-at-tech-company.html, I felt a bit nervous about retiring when everyone was telling me that I was 'too young.' As such, I cut my retirement a bit short and recently joined a new tech company
(ID# blinded in picture).
The Microsoft experience has been pretty interesting so far. The old and new commute only differ by a small distance shown below. In fact I had taken that trek a few times in the past, both walking during the summer months and driving during the rainy days when collaborating with Microsoft as an Intel employee.Speaking of firmware books, Jiming Sun's presentation https://talks.osfc.io/osfc-2024/talk/G8RDEX/ on firmware requirements from a CSP provided a unique perspective.
#1 firmware book? Fascinating metric. I'm not sure about the dataset used to generate that ranking. Although now at Amazon AWS, Jiming was a good collaborator during our joint tenure at Intel.
On the topic of books, on the Weds workday ahead of the T-day holiday I found another surprise when a coworker dropped by my touchdown/temporary office with one of the firmware books in hand https://link.springer.com/book/10.1007/978-1-4842-7939-7
I like books. And doors on offices are another fascinating phenomena after several decades of largely living in a cubicle.
Moving beyond the topic of books and continuing with co-workers theme, I see that another former Intel co-worker has left the blue building (Inside Blue to Outside Blue, departed the Blue Planet, gone from being an In-tel to an Out-tel?) is the other half of the 300-issued-patents duo of 2014 https://vzimmer.blogspot.com/2022/09/new-milestones.html who has a new opportunity https://natcast.org/natcast-announces-dr-robert-chau-svp-research
I guess the lure of the 'enhanced retirement package' of September drew him out, too? Maybe it was the new job title and mission which both sound pretty cool.I don't recall ever showing up in someone's LI experience listing. Interesting.
Although I started the blog grousing about weather maladies I really cannot complain so much. Another "Vincent Zimmer" has had it much worse recently https://www.youtube.com/watch?v=db9lTZiUgt8 it appears.
On the flip side, when I was leaving Intel, there was a session where the team was queried about what folks thought the imminent retirees would do post-Intel. One suggestion for me was a future as a patent attorney, and another suggestion was that I'd give a Ted Talk. On the latter suggestion it looks like another "Vincent Zimmer" beat me to the punch https://www.youtube.com/watch?v=eKdCsk3Yw-U. I think that disqualifies me for a future Ted Talk - speaker name hash collision rule :)
On the topic of the former suggestion of going back to school in the above-listed bon voyage meeting, I attended a Saturday conference https://con.racket-lang.org/ on the Racket programming language during my retirement windows between Intel and MS. During the lunch break-out at UW Kane Hall I expressed my interest in pursuing more formal graduate education when the PhD candidate to my left mentioned "yes, I'm in year 10 of my PHD program. I had to switch advisors and topics." Hmm. Given those types of statistics it would be a foot race between a PHD and Medicare eligibility for me. There were some interesting talks at the conference, though, including a keynote from the SICP https://en.wikipedia.org/wiki/Structure_and_Interpretation_of_Computer_Programs authors
And the conference shared other other bon mots on programming. Some may think Racket (and functional programming languages like Lisp in general) is so far from mainstream languages that there is little value in delving into these alt-langs, but I'm always surprised at the cross over of ideas from one language community to another or how a clean, pedagogic language can clarify your thinking on a subject.
Maybe I'll just continue the auto-didactic path and see if I can audit some uni courses of interest? I still remember Richard Ladner's https://www.cs.washington.edu/people/faculty/ladner late 1990's wisdom during my UW CS algorithms course - "What I teach you this quarter will become irrelevant soon, but what I can impart to you all is to teach you how to teach yourself and learn on your own." One of these AI sessions reminded me of this spirit in the slide below.
Speaking of gifts that keep on giving.....
Of course even Racket conference touched on AI, mostly via a spoof of LLMs by one UBC prof.
On a more serious approach to AI, though, I did attend a few IEEE-sponsored IEEE AI events on the UW campus and in Seattle, too.
I have to confess that the half-dozen LLM and AI texts & papers on my desk didn't receive as much, er, 'attention' (pun intended https://arxiv.org/abs/1706.03762), as I'd like to have applied during the 4 week retirement.
So this is nice symmetry. The blog opened with describing a talk to university students and ended with some wistful higher education sentiments. Not quite Finnegans' Wake of the first and last sentence running together, but good enough for JIT blog-writing I suppose.
I am still holding out using copilot or gemini or chatgpt or locally phi/llama/qwen/.... by way of ollama to create and/or polish these postings. I guess I like to maintain the raw, natural intelligence (or natural obtuseness) feel versus the polished AI-driven edits/creation. I am curious about other's thoughts on the topic. Maybe I'm just another John Henry versus the machine on this one....But in other activities these tools are amazing....Maybe just for this blog I've leave them out and keep it's artisanal feel :)
And so much for a November posting. Churn in the weather and the tech employment scene seem to be the themes of this posting.